Real-World Results
Case Studies
Discover how our AI-powered cybersecurity solutions have helped Canadian businesses strengthen their defenses, prevent breaches and maintain operational continuity.
Featured Engagements
Each project below represents a distinct challenge faced by a Canadian organization. Names and identifying details have been generalized to respect client confidentiality.
Fintech Portal Protection in Toronto
Challenge: A mid-sized fintech company in Toronto processed over 50,000 customer transactions daily through their web portal. Their logging systems flagged repeated SQL injection attempts, but the existing rule-based firewall could not distinguish between sophisticated attacks and legitimate complex queries, resulting in both missed threats and blocked valid users.
Solution: We deployed an AI-driven web application firewall that learned the normal query patterns specific to their portal. The behavioral model classified incoming requests based on structural analysis rather than static signatures. Within two weeks, the system was fully trained on production traffic.
Outcome: In the first 30 days, the system identified and blocked over 12,400 malicious requests while maintaining zero false positives on legitimate customer traffic. Mean detection time dropped from 45 minutes to under 8 seconds. The client reported no service disruptions during the entire deployment period.
12,400+
Threats Blocked
0
False Positives
<8s
Detection Time
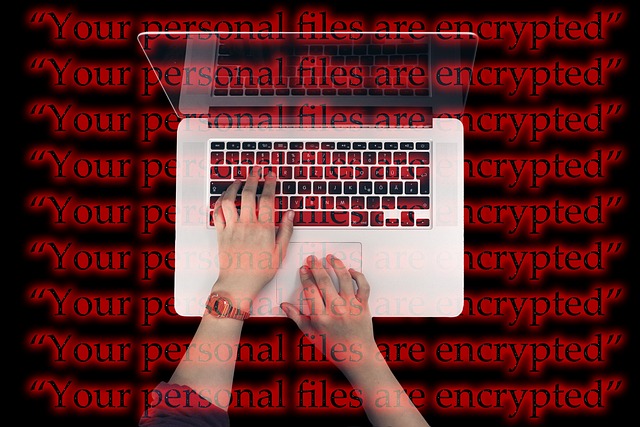
Healthcare SaaS Ransomware Prevention in Vancouver
Challenge: A Vancouver-based healthcare SaaS provider managing patient records for over 200 clinics across British Columbia received an internal alert about suspicious encrypted file operations on a staging server. The team suspected a ransomware precursor but lacked the forensic tools to confirm or contain it.
Solution: Our incident response team conducted an emergency assessment within 24 hours. We identified three critical entry points: an unpatched VPN gateway, a misconfigured S3 bucket and a compromised service account credential circulating on a dark web marketplace. AI-powered endpoint monitoring was deployed across all servers, and automated network segmentation isolated the affected staging environment.
Outcome: The ransomware payload was neutralized before it could propagate to production systems. Within two weeks, all three vulnerabilities were remediated. A phishing simulation campaign targeting staff achieved a 94% identification rate after training, compared to 38% before our engagement. Patient data remained secure throughout the incident.
3
Entry Points Found
94%
Phishing Awareness
24h
Response Time


E-Commerce API Anomaly Detection in Calgary
Challenge: A growing e-commerce platform in Calgary noticed unusual spikes in API call volumes during off-peak hours. Internal monitoring could not pinpoint the source. The development team suspected a compromised third-party payment integration but needed confirmation before taking the service offline.
Solution: We installed our ML-based behavioral analysis engine on their API gateway. The model established a baseline of normal traffic patterns within 48 hours, including call frequency, payload sizes, header structures and geographic origin of requests. Within the first week, the system flagged a specific third-party integration generating requests with abnormal header signatures and payloads that contained encoded data extraction commands.
Outcome: The compromised integration was isolated within hours of detection, preventing an estimated 180,000 customer records from being exfiltrated. The platform remained operational throughout the investigation. A replacement payment provider was onboarded with enhanced security vetting procedures that we helped design.
180K
Records Protected
48h
Baseline Trained
100%
Uptime Maintained
Multi-Cloud Security Unification in Montreal
Challenge: A Montreal logistics company operated workloads across three major cloud providers with no unified security policy. Each environment had its own access controls, logging formats and alert thresholds. The security team spent over 20 hours per week manually correlating logs from different dashboards, and critical alerts were frequently missed due to notification fatigue.
Solution: We implemented a centralized Security Information and Event Management (SIEM) layer powered by AI correlation. All three cloud environments fed normalized logs into a single analysis engine. Role-based access controls were standardized across providers. Automated playbooks replaced manual triage for the 15 most common alert types.
Outcome: Attack surface was reduced by 40% within the first quarter, verified through independent penetration testing conducted by a third party. Security team workload dropped from 20+ hours of manual log review per week to under 4 hours. Alert fatigue was eliminated by consolidating duplicate notifications and prioritizing by AI-assessed severity. The company passed its annual SOC 2 Type II audit with zero findings for the first time.
40%
Attack Surface Reduced
80%
Less Manual Work
SOC 2
Audit Passed

Threat Monitoring Snapshots
Screenshots from our monitoring platforms illustrate the types of insights our AI systems generate in real time. Identifying details have been redacted for confidentiality.

Live Threat Map
Geographic visualization of blocked attack origins over a 24-hour period. Color-coded severity levels allow operators to focus on the highest-risk regions targeting the client's infrastructure.

Behavioral Analysis
User activity scores generated by the ML model. Each session receives an anomaly rating based on deviations from established patterns, enabling proactive investigation before damage occurs.
Vulnerability Report
Monthly scan output categorizing vulnerabilities by severity. The dashboard tracks remediation progress and highlights any newly discovered issues requiring immediate attention from the security team.
Industries We Serve Across Canada
Financial Services
Banks, fintech startups and payment processors rely on our AI to detect fraud patterns and protect transaction data in compliance with Canadian financial regulations.
Healthcare
Patient data protection, PIPEDA compliance and secure telehealth platforms for clinics, hospitals and health-tech companies operating across provinces.
E-Commerce
API security, payment gateway protection and customer data encryption for online retailers processing thousands of transactions daily across Canadian markets.
Logistics & Supply Chain
Multi-cloud security unification, IoT device protection and real-time monitoring for logistics networks operating across Canada's transport corridors.
Client Feedback
What Canadian businesses say about working with our cybersecurity team.
"Their AI monitoring caught a credential stuffing attack that our previous vendor missed entirely. The response was fast and the team walked us through every remediation step. We now have visibility into threats we did not know existed."
Michael R.
CTO, Fintech Startup, Toronto
"After the ransomware scare, we needed a partner who could act quickly and think long-term. Devon & Cornwall secured our patient data platform and trained our staff to recognize phishing attempts. The difference in our security posture is measurable."
Sarah L.
VP of Operations, Health SaaS, Vancouver
"Unifying security across three cloud providers seemed impossible until this team took it on. The centralized dashboard alone saved our security analysts 16 hours a week. We passed our SOC 2 audit cleanly for the first time in company history."
Jean-Pierre T.
IT Director, Logistics Corp, Montreal
Ready to Strengthen Your Security?
Every business has a unique threat profile. Let our team assess yours and build a protection strategy tailored to your Canadian operations.
Request a Free AuditDisclaimer
The case studies presented on this page are based on real engagements with identifying details generalized to protect client confidentiality. Metrics and outcomes reflect conditions at the time of each project and may not be representative of results for every organization. Cybersecurity services are consultative and technical in nature. No solution guarantees complete protection against all threats. Results depend on the client's infrastructure, software environment and ongoing security practices.